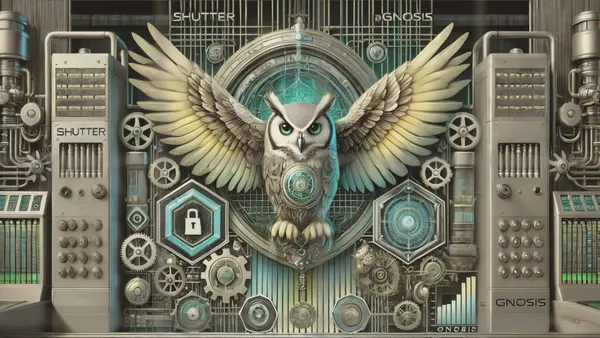
We're excited to announce that the Shutter protocol will soon be available on Gnosis Chain mainnet, enhancing blockchain security and fairness. This integration will revolutionize transaction security and advance decentralized finance (DeFi).
The Shutterized Gnosis Chain will go live on Thursday, the 11th of July, 2024!
Shutter Will Be Protecting Gnosis Chain Users from Malicious MEV
Maximal Extractable Value (MEV) attacks are manipulative practices that exploit transaction ordering within a block to maximize financial gains for malicious actors. These attacks act as an invisible tax on transactions, inflating costs for traders and undermining the integrity of DeFi.
Shutter employs threshold encryption to shield the transactions. Encrypting transactions before they enter the public mempool prevents malicious actors from exploiting them to their advantage. Participating validators on the Gnosis Chain will commit to including these encrypted transactions, making it virtually impossible for front runners to interfere. This level of protection ensures that end-users are shielded from financial losses and market manipulation, maintaining the integrity of the decentralized system.
Steps Taken Include Alpha Keyper Testnet and Full Chiado Testnet Implementations
Our journey towards this integration has been well planned and executed, starting with the successful deployment of the alpha Keyper testnet on Chiado. This initial phase focused on establishing the essential contracts and Shutter Keyper client, laying the foundation for more comprehensive implementations.
Following the alpha phase, we launched the full Shutterized Chiado testnet, marking the first live integration of the Shutter protocol on a testnet. This testnet represents the culmination of our combined efforts with the Gnosis and Nethermind teams to refine and perfect the processes, ensuring seamless operation and robust security. These milestones are crucial as we prepare for the mainnet launch, where we will bring a robust threshold encrypted mempool to the Gnosis Chain, transforming it into a safer and more reliable environment for all users.
How the Shutterized Gnosis Chain Will Premiere
As the mainnet implementation is still a few weeks away, we will provide updates on the progress made prior to the launch.
We will host a couple of Shutter Community Calls to share updates with the community. The first one, where we'll discuss the Shutterized Gnosis Chain, will be tomorrow, June 20th!
All teams—Shutter, Gnosis, and Nethermind—need to continue with the ongoing development. The initial implementation will be somewhat limited to ensure smooth operation, with a more robust setup available after the launch.
Validators and Keypers
The Gnosis Chain validators and Keypers are crucial entities influencing users' experience with encrypted transactions.
The initial Keyper set will be limited in scope—it will consist of 7 node operators—and a more decentralized set with 21 node operators is expected in the following weeks.
Also, a smaller set of validators will be onboarded at the launch, to reduce risks and allow for sufficient testing, so getting encrypted transactions included in blocks could take a bit more time than usual. However, with the Nethermind client being a majority client among the Gnosis Chain validators, we expect to gain more adoption among the validators quite soon.
And, of course, make sure you catch the "Advancing base layer neutrality: The Launch of Shutter's Encrypted Mempool on Gnosis Chain" talk by Frederik Lührs at 13:25 on the Silver Hall stage at EthCC!
Setting a New Standard for MEV Protection
Shutter's approach to tackling MEV attacks is both distinct and effective. Integrating our protocol directly into the blockchain network eliminates the opportunities for manipulators to exploit transaction information. Our protocol involves using a threshold-encrypted mempool, which ensures that transactions remain encrypted until they are securely included in a block.
Technical Integration Details of Shutter on Gnosis Chain
Gnosis Chain, known for its community-driven approach and robust security, is taking a significant leap forward by integrating Shutter's encryption protocol. This integration enhances the chain's resilience against malicious MEV attacks and improves the user experience.
How Shutter Integrates with Gnosis Chain
- Keyper Nodes and Threshold Encryption: At the heart of the Shutter protocol are the Keyper nodes, which manage the generation and issuance of encryption and decryption keys. These nodes utilize a Distributed Key Generation (DKG) protocol to ensure that no single node can decrypt a transaction independently, thereby maintaining a decentralized and secure reveal process.
- Sequencer Contract: The sequencer contract on the Gnosis Chain acts as the central hub for managing encrypted transactions. When a user submits a transaction, it is encrypted using the public key generated by the Keyper nodes and then sent to the sequencer contract. This contract maintains a list of transactions to be processed in the arriving order and schedules them for inclusion in a future block.
- Validator Commitment: Validators on the Gnosis Chain play a crucial role in the Shutter integration. They commit to including and correctly ordering encrypted transactions within the blocks they produce. This commitment is essential to maintaining the integrity of the encrypted mempool and ensuring that transactions are protected from front running and other MEV attacks.
Detailed Process Flow
- Transaction Encryption
- Users encrypt their transactions using the public key provided by the Keyper nodes.
- Alternatively, users can send plaintext transactions to a trusted JSON RPC endpoint, which handles the encryption process.
- Submission to Sequencer Contract
- Encrypted transactions are submitted to the sequencer contract.
- The sequencer contract maintains an ordered queue of these transactions, defining the processing order for inclusion.
- Decryption and Block Inclusion
- After the encrypted transactions have been included in a block, the Keyper nodes generate the corresponding decryption keys.
- Validators retrieve the encrypted transactions from the sequencer contract and use the decryption keys to decrypt them.
- The decrypted transactions are then included in the block in the order determined by the sequencer contract.
- Ensuring Fairness and Security
- Threshold encryption ensures no single party can manipulate the transaction order or content.
- Validators and Keyper nodes work together to maintain the integrity and confidentiality of transactions until they are securely included in a block.
Benefits for the Gnosis Chain
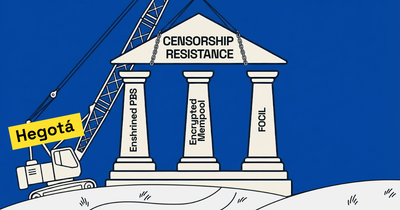
- Enhanced Security: By integrating Shutter, Gnosis Chain significantly enhances its security against MEV attacks. Encrypted transactions prevent malicious actors from exploiting transaction information for personal gain.
- Increased Trust: Shutter's decentralized encryption protocol aligns with Gnosis Chain's commitment to decentralization and trustlessness, boosting user confidence.
- Operational Efficiency: The seamless integration of the sequencer contract and Keyper nodes ensures that encrypted transactions are processed efficiently without adding significant network overhead.
- Censorship Resistance: Validators' commitment to processing encrypted transactions as per the sequencer's order adds a layer of censorship resistance, ensuring that no transactions are unfairly excluded.
Technical Specifications
- Keyper Set Size: The initial deployment includes 7 Keyper nodes, ensuring a robust encryption key generation process while still allowing good performance monitoring and the ability to apply bug fixes quickly. This is in the spirit of progressive decentralization as the Keyper set will expand.
- Threshold Cryptography: Utilizes advanced cryptographic techniques to ensure that a minimum number of Keyper nodes must collaborate to decrypt transactions, preventing single points of failure.
- JSON RPC Endpoint: Provides a user-friendly interface for transaction submission, with built-in encryption capabilities to simplify the process for end-users.
Future Enhancements
As we look towards the future, several enhancements are planned to integrate Shutter with Gnosis Chain further:
- Client Libraries: Development of client libraries to facilitate local encryption, reduce reliance on the JSON RPC endpoint, and enhance security.
- Validator Incentives: Implementing incentive mechanisms to encourage more validators to participate in the encrypted transaction processing, ensuring robust network security.
- Expanded Keyper Set: The number of Keyper nodes will be increased to decentralize the encryption process further and enhance the protocol's security.
A Vision for the Future
This integration is only the beginning. The Shutter protocol is aimed to extend across the Ethereum ecosystem, combating malicious MEV attacks and reinforcing the core principles of blockchain technology: openness, neutrality, and resistance to censorship. We envision a future where Shutter's technology is widely adopted across various blockchain networks, continually improving the security and fairness of DeFi environments.
Join the Revolution to Defend the Crypto Realm
Stay tuned for more updates as we enhance the Gnosis Chain with Shutter technology. Join us on this journey and be a part of the revolution, defending the crypto realm.
Start trading safely on Gnosis Chain on July 11th! Experience the enhanced security and fairness of Shutterized transactions.
Follow us on X-Twitter, visit the Shutter Forum, and join our community on Discord to learn more about how Shutter works and stay updated on our progress.

![Shutter Network at EthCC[7]](https://storage.ghost.io/c/c5/d9/c5d9b75d-ef42-4dd6-acc9-8f6f3b90736d/content/images/size/w250/2024/07/shutter_at_ethcc_7.jpg)