Blog post series about MEV for beginners.
This MEV explainer series for beginners serves you and the crypto community to dive into the "dark forest" of the maximal (formerly known as miner) extractable value (MEV) world and hopefully lighten up or refresh your knowledge about the entire problem we are all in. Let's go!
How It All Started
On 10th April 2019, eight research fellows from Cornell University, University of Illinois, Carnegie Mellon University and ETH Zürich kicked off the journey into the dark forest. A foggy journey to find a way that helps the entire Ethereum community to make the maximal extractable value (MEV) problem distinct.
Throughout the journey, other community members jump onboard to fight front runners and malicious MEV. Great teams like Paradigm, Flashbots and individuals like samczun and probably hundreds of others are actively researching and building weapons against front runner bots, corrupt miners and validators. Let's not forget MEV searchers! The ones who try to find liquidation opportunities by also using front running strategies.
If we cannot win this game, MEV will harm the user experience and slow down global crypto adoption.
Finding a weapon against MEV is good but educating the community is essential! You have probably already been a victim of those front runners, but you haven't noticed yet.
How could you notice that a front runner reordered and manipulated transactions for their profit? It is almost impossible for non-techy crypto users! Why? You cannot see how a bad actor runs their miners or validators, and it is invisible to you how they process, validate and execute transactions as they run custom software.
As you are already here to learn more about MEV, let's create awareness of how malicious MEV can manipulate transactions in the mempool. Ready?
The Smelly Fishers Catching Transactions In The Mempool

In this blog post, I'll dive into transactions and the mempool and scratch the surface without unloading all the tech-terms into your brain 🧠. It will help you to understand the primary mechanism of why maximal extractable value (MEV) and front running are possible. Let's move on!
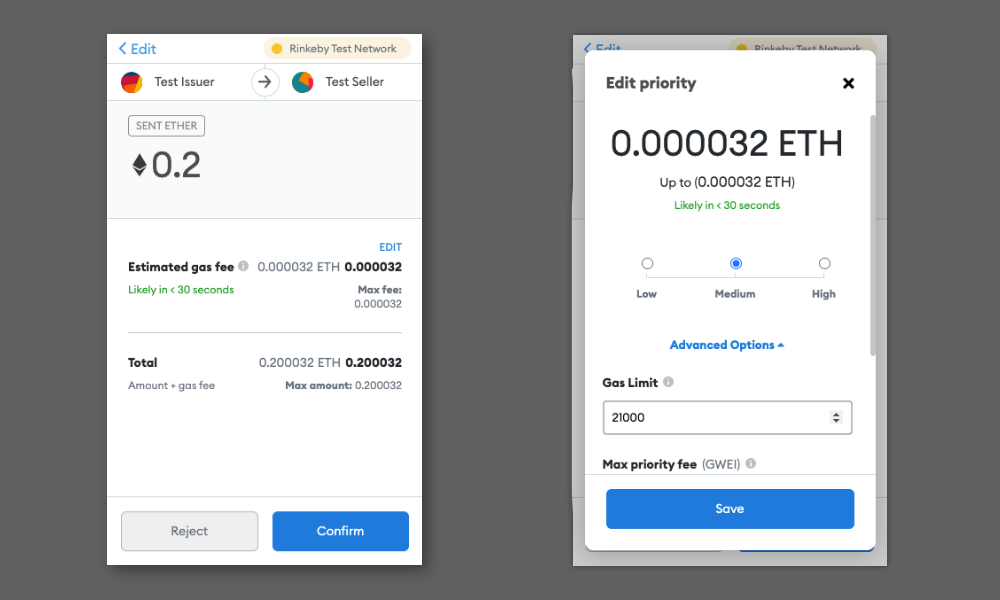
I assume you have sent ETH or tokens from one Ethereum account to another, haven't you? If not, head over to MetaMask or an alternative Ethereum wallet and create your Ethereum address. As soon as you are ready to submit the transaction finally, you'll see the estimated gas fees. Confirm and wait for miners and validators to fish the transaction. But wait:
What are transaction fees, and why do they exist?*
If you want to cross a river with a ferryman, you have to pay him a fee to take you to the other side. He is doing the work and makes his living with his ferry. There is demand and supply, and you pay the fee, don't you?
Let's say we have John; he runs a miner who is doing the heavy work. Like the ferryman, John wants to make some ETH for his work, too! John's computer (the miner) executes your transaction, and for this work, you pay a fee. The unit for the fee is called Gas. Why do you call it Gas? This was one of my first questions when I first learned about Ethereum, too. ETH is the oil that the miners receive as a reward. And the reward for executing a transaction is gas which is measured in Gwei. Why Gwei? It is the smallest unit of Ether. And what is the "g" standing for? One Gwei equals 1,000,000,000 wei. One giga-wei! Next time you send a transaction, you know what the number stands for. By the way, the smallest unit for bitcoin is called satoshi.
Would you invest in hardware to store, process and validate Ethereum transactions for free? Nope!
John is incentivized by the two types of rewards – The block reward and the transaction fee reward. That's the economic game we are in. The fees provide essential spam protection for the blockchain network!
For some actors, these rewards are not sufficient enough, and they want to maximize their profit. They attack with a front run. (I'll explain how these bad actors increase profit in the upcoming blog post dedicated to front running attack types.)
What happens after I have sent an Ethereum transaction?
I have some $FISHY tokens. I want to swap 100 of them for some $JABBA tokens on Uniswap. And John wants to steal the same swapped $JABBA tokens. John (in our case, John plays a front runner) with his miner is running one or more nodes. A node is a piece of software running on a computer connected to other computers within the blockchain network. That's the setup you can picture? Great! Let's continue.
As soon as I submit the transaction, including 100 $FISHY tokens and a gas fee of 0.1 ETH (That's pricey 🤑, I know. I want the $JABBA tokens so badly!), my browser wallet sends the transaction to a server which is connected to my wallet. This server (a node) broadcasts all the incoming transactions of wallets connected to the blockchain network. John's miner nodes are now also aware of the $FISHY tokens. He wants to catch this transaction and front run it!
Before John can front run my transaction, his node needs to queue all transactions in a lake of transactions. Transactions are not put in blocks right away. That's this blockchain thingy. It's not a part of this blog post, and I'll skip it here.
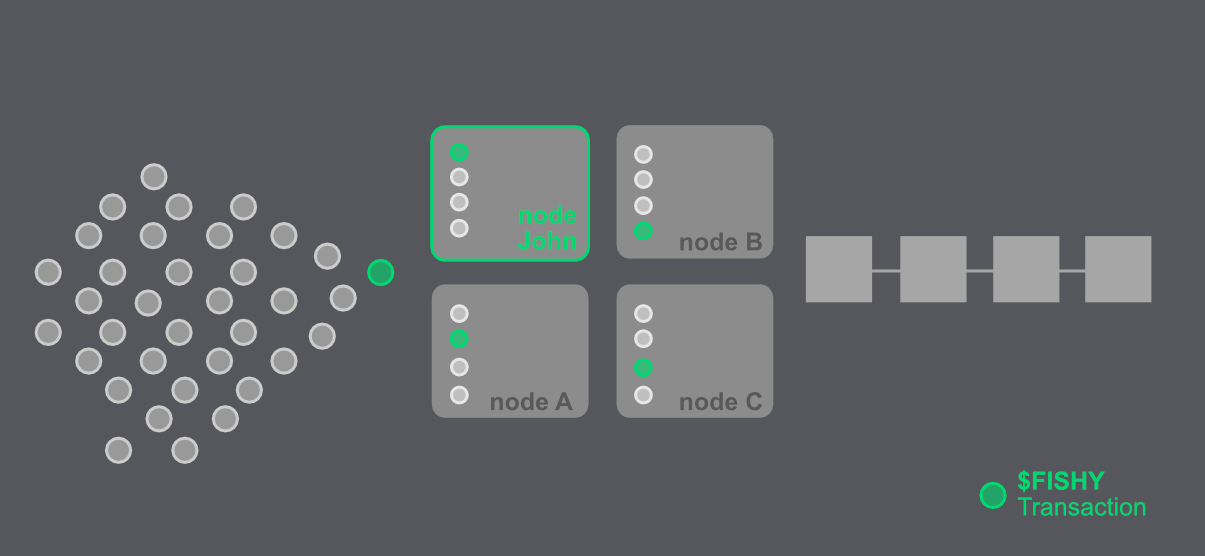
Ok, my 100 $FISHY swap transaction is waiting in the so-called mempool of John's node. What can he do with it? He wrote custom software that checks transactions in the mempool. These checks look for specific transaction attributes. In my case, one of those checks looks for $FISHY token transactions! The software sorts and orders all the transactions according to John's rules and prioritizes my $FISHY tokens to the top of the queue! It depends on his rulesets which kind of front running attack is executed. My transaction can be 🦹🏻♂️ time-bandit, 💹 arbitraged or 🥪 sandwiched (more details in my next blog post how those attacks work). Boom, I got fished!
So Why Is Front Running Bad?
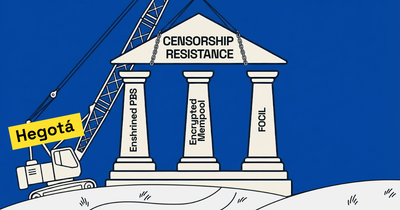
John can manipulate transactions because of the open public permissionless ledger infrastructure. The content of transactions is transparent to all actors of the infrastructure. This is the reason why John can observe transactions and extract profitable ones for him. He can steal your transaction, make you pay more fees and prevent your transaction to be executed. These front running types are bad as we users are losing without knowing that we are taken advantage of. It is not a fair market and we need to do something about it.
The question is – Is there a way we can hide transaction details, so John cannot sort and order transactions for his favor? The answer is – yes, there are ways how we at Shutter can solve the MEV front running problem. Read our in-depth blog post on how we prevent front running.
I explained why you have to pay for transaction fees and why miners are incentivized to maximize their profits in this post. You understand that bad actors can manipulate transactions in the mempool with custom software solutions.
That's all about it for today. Part 2, about front running attacks, is in the making!
Did you learn something new in the post? The Shutter team would be thankful if you spread the word and share the post via X-Twitter!
*For the crypto cracks! I know that with EIP-1559 the transaction fee mechanism changed.